I'm all for whistle-blowers, rah-rah. BUT !
Providing $taxpaying $voters relevant information that might embarrass incompetent or corrupt government officials is quite different from
betraying heroic covert intelligence assets, subjecting them to murder and or torture.
The former informs the electorate.
The latter damages U.S. ability to gather important intelligence. Is there a more egregious, senseless, self-defeating form of betrayal?
Here's a hint.
Such outright betrayal is a transcendent disgrace. It is potentially, and has proven to be in multiple cases,
the most severe punishment imaginable, for those that have earned much, much better, our unwavering respect & gratitude.
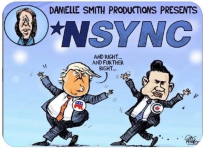
in context of Val Plame & Ambassador Wilson:
"Even though I'm a tranquil guy now at this stage of my life; I have nothing but contempt and anger for those who betray the trust by exposing the name of our sources. They are in my view the most insidious of traitors." GHWB
Former CIA head, U.S. President Bush (the elder), at the dedication of the George Bush CIA HQ in 1991 [ source: NBC-TV
Meet The Press ]
I only vaguely remember how Novak reported on Valarie Plame being CIA, ruining her cover, and making is too dangerous for her to travel anymore.
I think Armitage and Libby were the source of the leak.
But I do not think Snowden named assets, but systems instead.
{...
Edward Snowden revealed extensive global surveillance programs conducted by the NSA and its international partners, exposing how governments collect and monitor digital communications on a massive scale.
Key Revelations:
PRISM Program: Snowden disclosed that the NSA had direct access to data from major tech companies, including Google, Facebook, Microsoft, Apple, Yahoo, Skype, YouTube, and Dropbox. This program allowed the NSA to collect emails, documents, photos, and other communications without individual court orders, effectively giving intelligence agencies a backdoor into global digital communications.
XKeyscore: This tool enabled the NSA to search and analyze vast amounts of internet data in real time, including emails, browsing histories, and online activity, making it possible to track individuals’ online behavior with minimal oversight.
Tempora: Snowden revealed that the British intelligence agency GCHQ tapped into fiber-optic cables to intercept and store global internet traffic, sharing this data with the NSA. This program collected emails, social media posts, and phone records on a massive scale.
Other Surveillance Tactics: Documents showed that the NSA used “method interdiction” to intercept packages, installing malware or backdoor hardware before forwarding them to recipients. The NSA’s ANT division developed technology capable of monitoring and even altering data on offline computers.
Telephony Metadata Collection: Snowden disclosed that companies like Verizon were compelled to hand over metadata from phone calls, including numbers dialed, call durations, and locations, covering both domestic and international communications.
Broader
Snowden’s leaks highlighted the
global reach of intelligence agencies, the cooperation between the NSA and the Five Eyes alliance, and the involvement of telecommunications companies and foreign governments in mass surveillance. His revelations sparked worldwide debates on privacy, government transparency, and the ethics of surveillance, leading to legal challenges and reforms in some countries.
...}